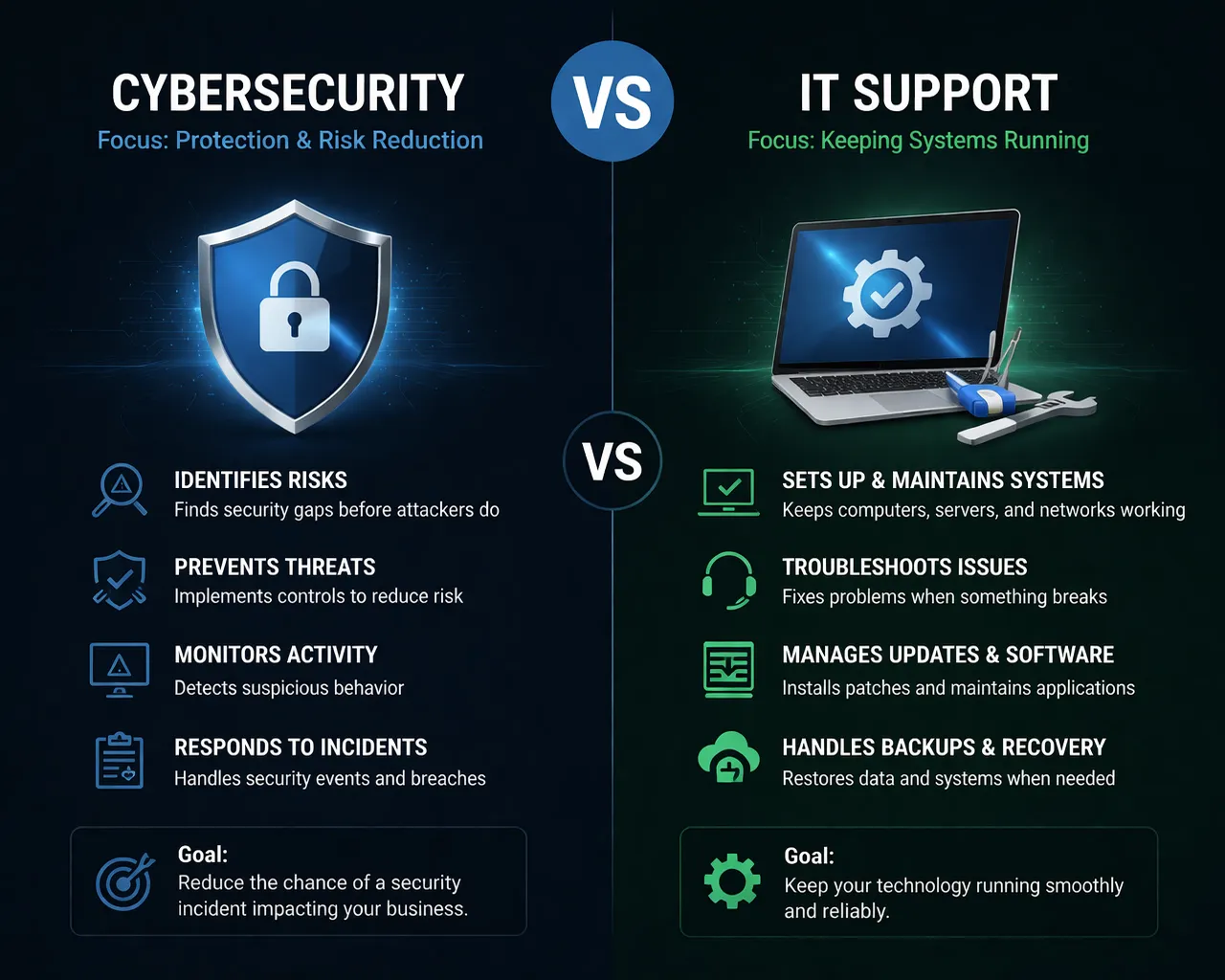
Many organizations today rely on Managed Service Providers (MSPs) and Managed Security Service Providers (MSSPs) to operate their technology and security environments. These providers are essential partners, and they play a critical role in keeping systems running and protecting businesses from threats.
However, many companies still struggle with an important question:
Are we investing in the right technology and security priorities?
That’s where an independent technology and cybersecurity review can help.